How Do Security Companies Get Contracts: Strategies and Tips
In the competitive world of security services, securing contracts is crucial for success. This article will discuss various strategies and tips for security companies to help them land lucrative contracts, from networking and marketing to crafting winning proposals and retaining clients.
Building a Strong Company Profile
To attract clients, security companies need a solid company profile. This includes having well-trained staff, proper certifications, and showcasing expertise in various security services. By building a strong company profile, companies can demonstrate their credibility and reliability, making them more attractive to potential clients.

Networking and Establishing Relationships
Industry events: Attending conferences, trade shows, and other industry events can help security companies meet potential clients and establish valuable relationships. These events can also provide insights into the latest trends and technologies.
Online platforms: Participating in online forums and groups related to the security industry can help build connections and demonstrate expertise.
Local business associations: Joining local business associations and chambers of commerce can provide opportunities to network with local businesses and organizations that may require security services.
Creative idea – Offer refreshments: While it’s not always possible to speak directly to the decision-maker, like the property manager, it’s important to make a positive impression on other staff members such as leasing agents or assistant managers. By bringing food or refreshments, your security company will stand out in their minds, increasing the likelihood that they will recommend you to the property manager. This thoughtful gesture can leave a lasting impression and help build relationships with potential clients. This idea was brought here by chickenonfireworks from Reddit:
Marketing and Advertising Strategies
Targeted marketing: Focusing on specific industries or target markets can help security companies tailor their marketing efforts and reach the right audience.
Social media presence: Maintaining an active social media presence can help security companies engage with potential clients and showcase their expertise, success stories, and company culture.
Case studies and testimonials: Sharing success stories and testimonials from satisfied clients can help demonstrate a security company’s value and effectiveness.
Partner with complementary businesses: Collaborate with businesses that offer complementary services, such as property management companies, event organizers, or construction firms, to create mutually beneficial referral partnerships.
Crafting a Winning Proposal
A well-crafted proposal is essential to securing a contract. Security companies should ensure their proposals are clear, concise, and tailored to the client’s specific needs. This includes outlining the scope of services, pricing, and a detailed plan of action.

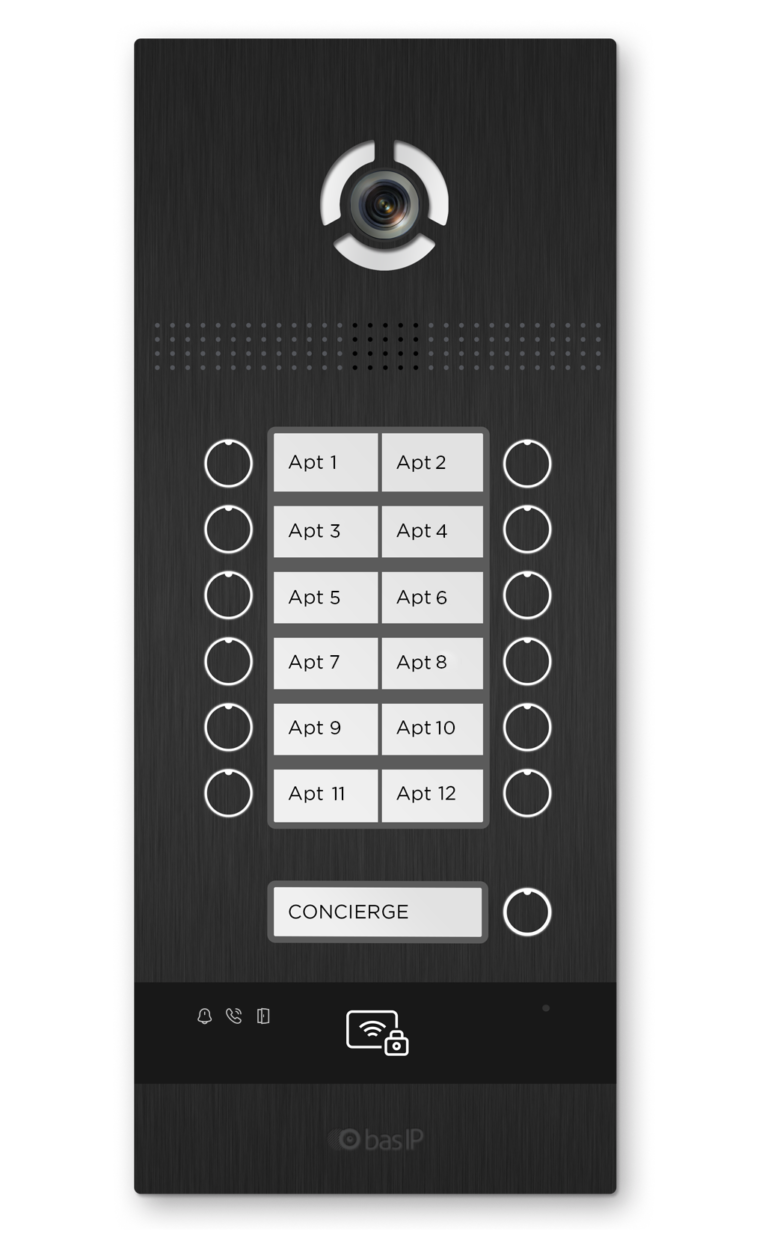
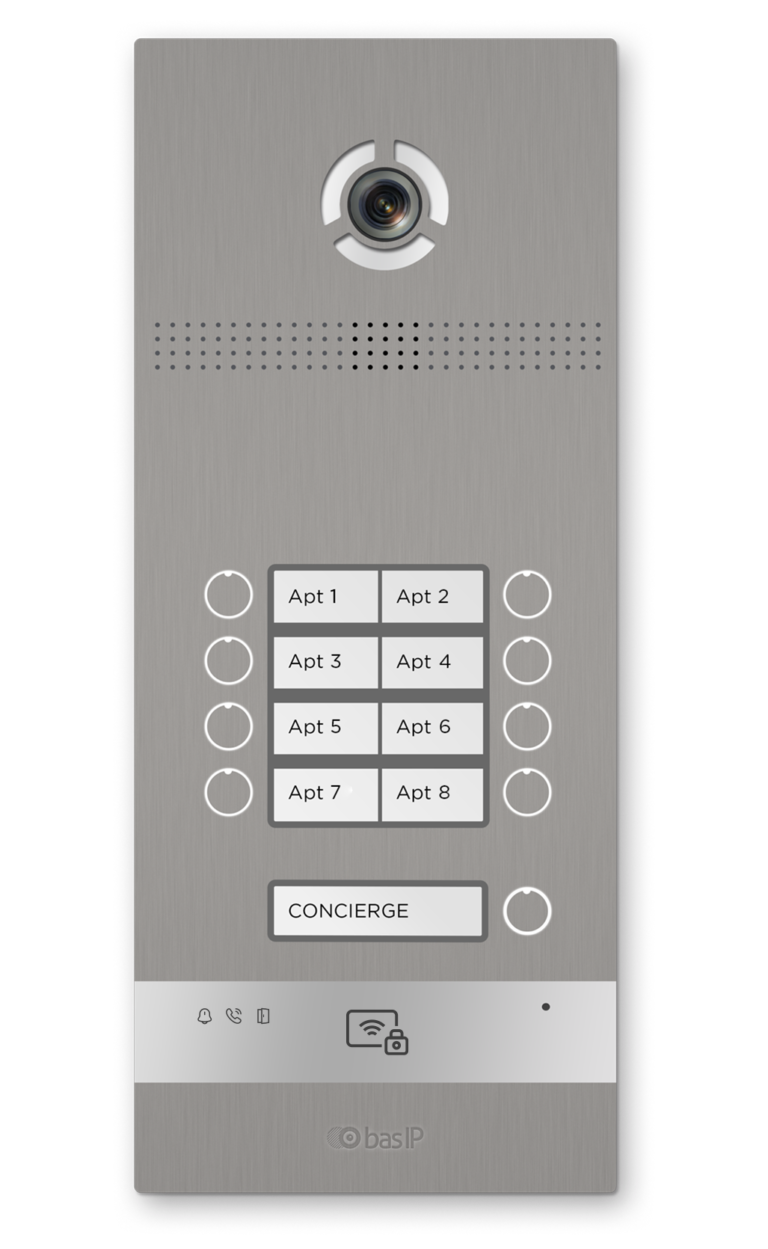
Offering advanced technology, such as IP intercom systems with cutting-edge features, can significantly improve the percentage of signed contracts compared to offering outdated, mass-market analog intercoms. For example, IP intercom systems with features such as multi-apartment video calls, integration with third-party devices, and mobile app control would be much more appealing to potential clients.
Offer competitive pricing and service packages
Analyze the competition and offer competitive pricing and service packages that cater to different client needs. Providing flexible options can attract a wider range of clients.
Target specific industries or niches
Focus on a specific industry or niche market where your security company can excel, such as healthcare, education, or retail. Specializing in a particular area can help differentiate your company from competitors and make you the go-to choice for clients in that industry.
Winning Proposal Example
[Your Company Logo]
[Your Company Name]
[Your Company Address]
[City, State, Zip Code]
[Phone Number]
[Email Address]
[Website]
[Date]
[Client Name]
[Client Company Name]
[Client Address]
[City, State, Zip Code]
Subject: Security Services Proposal
Dear [Client Name],
Thank you for considering [Your Company Name] for your security service needs. We understand the importance of ensuring the safety and security of your [facility/property/event]. With our extensive experience in providing professional security services, we are confident that we can meet your specific requirements and exceed your expectations.
This proposal outlines our understanding of your security needs, the scope of our services, and our proposed pricing.
Overview of Client’s Security Needs
Based on our discussions, we understand that you require [security services description, e.g., 24/7 security personnel, intercoms, access control, CCTV monitoring, etc.] for your [facility/property/event]. Your primary concerns include [list the client’s main security concerns, e.g., theft, vandalism, unauthorized access, etc.].
Scope of Services
Our proposed security solution includes the following services tailored to your specific needs:
[Service 1]: [Brief description of the service, e.g., Deployment of professionally trained and licensed security guards to patrol the premises, monitor access points, and respond to security incidents.]
[Service 2]: [Brief description of the service, e.g., Installation and maintenance of a comprehensive CCTV system with remote monitoring capabilities.]
[Service 3]: [Brief description of the service, e.g., Implementation of an access control system to prevent unauthorized entry and ensure only authorized personnel have access to restricted areas.]
Proposed Security Team
We will assign a dedicated security team to your [facility/property/event], led by an experienced security manager who will serve as your primary point of contact. Our security personnel undergo rigorous background checks, receive comprehensive training in security procedures, and hold all necessary licenses and certifications.
Implementation Timeline
Upon acceptance of this proposal, we will initiate the following implementation timeline:
[Phase 1]: [Brief description of phase 1 activities, e.g., Site assessment and security plan development, with an estimated completion date.]
[Phase 2]: [Brief description of phase 2 activities, e.g., Security system installation and testing, with an estimated completion date.]
[Phase 3]: [Brief description of phase 3 activities, e.g., Security personnel deployment and commencement of services, with an estimated start date.]
Pricing
Our proposed pricing for the security services outlined in this proposal is as follows:
[Service 1]: [Price, e.g., $X,XXX per month]
[Service 2]: [Price, e.g., $X,XXX one-time setup fee and $XXX per month for maintenance and monitoring]
[Service 3]: [Price, e.g., $X,XXX per month]
Please note that the pricing above is valid for 30 days from the date of this proposal.
We appreciate the opportunity to present our proposal and look forward to working with you to ensure the safety and security of your [facility/property/event]. If you have any questions or require further information, please do not hesitate to contact us.
Thank you for considering [Your Company Name] as your security service provider.
Sincerely,
[Your Name]
[Your Title]
[Your Company Name]
Client Retention and Referrals
Satisfied clients are more likely to refer a security company to their network, leading to more contracts. Companies should focus on building strong relationships with existing clients by providing exceptional service, regular communication, and being responsive to their needs.
| Category | Fact/Statistic |
|---|---|
| Customer Retention | It costs 6-7 times more to acquire a new customer than to keep an existing one. |
| Customer Experience Impact | By 2020, customer experience will overtake price and product as the key brand differentiator. |
| Customer Advocacy | Responding to a customer complaint can increase customer advocacy by 25%. |
| First Contact Resolution Impact | 67% of customer churn is preventable if the customer issue is resolved at the first engagement. |
| Unhappy Customers | 1 in 26 unhappy customers complain; the rest churn. |
| Profitability Impact | A 5% increase in customer retention can increase a company’s profitability by 75%. |
| Negative Experience Sharing | Customers are 2x more likely to share a bad customer service experience on social media than a good one. |
| Customer Loyalty Impact | 93% of customers are likely to make repeat purchases with companies that offer excellent customer service. |
Conclusion
Securing contracts is key to the success of any security company. By implementing the strategies and tips discussed in this article, security companies can strengthen their chances of landing lucrative contracts and growing their business. From building a strong company profile to networking and marketing, these efforts will pay off in the long run.